In Windows Server 2016, Windows Firewall is enabled by default. This allows all outgoing traffic to any destination or port, but limits incoming traffic based on specific rules. We’ll cover how to configure Windows Firewall with Advanced Security by demonstrating how to open it through both the GUI and PowerShell, followed by a demonstration of how to create a custom firewall rule.
This post is part of our Microsoft 70-744 Securing Windows Server 2016 exam study guide series. For more related posts and information check out our full 70-744 study guide.
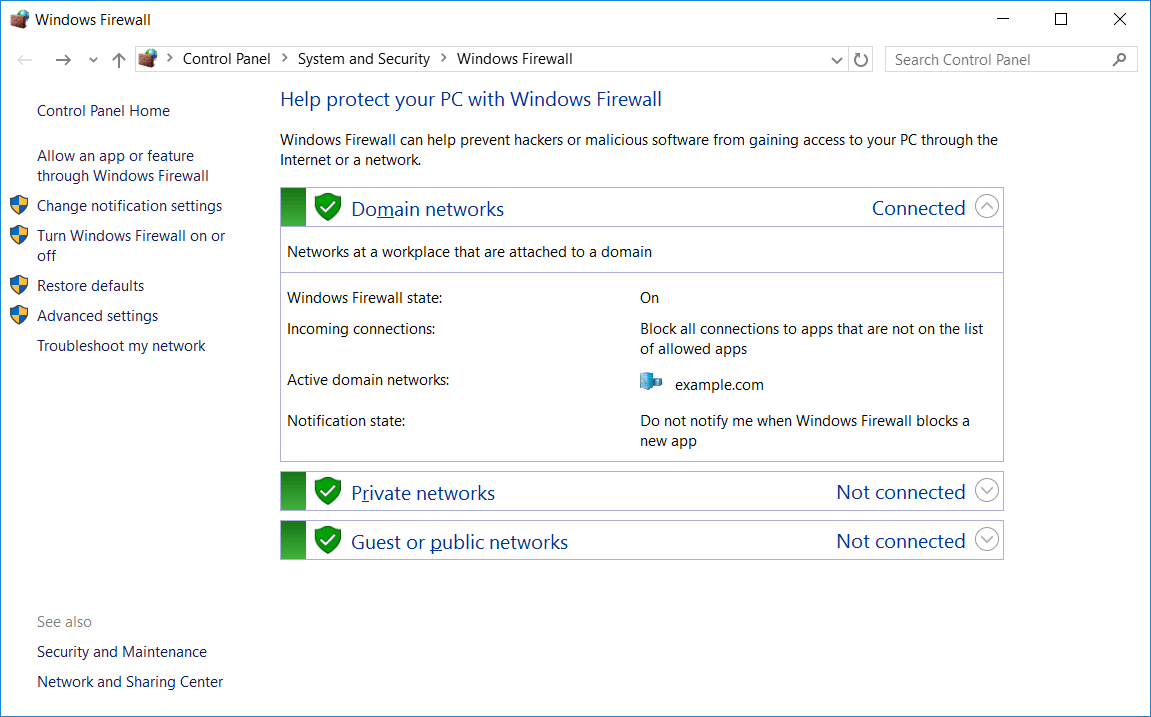
Windows Firewall – Control Panel
Basic Windows firewall settings can be modified through Control Panel > System and Security > Windows Firewall, as shown below. This interface can also be accessed through PowerShell or Command Prompt by entering ‘firewall.cpl’.
From here we can graphically view the status of the firewall for the domain, private, and public profiles. These different profiles are used depending on your current network connection. For example if you’re joined to an Active Directory domain, the rules applied in the domain profile will be used, while if you’re connected to a public wireless network the settings in the public profile will be used.
In this example, we can see the domain profile is listed as connected, as we’re currently connected to the example.com domain.
The tasks that can be completed here are shown in the menu on the left, we don’t go into detail here as we’re mainly going to be dealing with the advanced settings. To access the advanced settings, you can select the advanced settings link from this menu on the left from within Windows Firewall.
Windows Firewall with Advanced Security
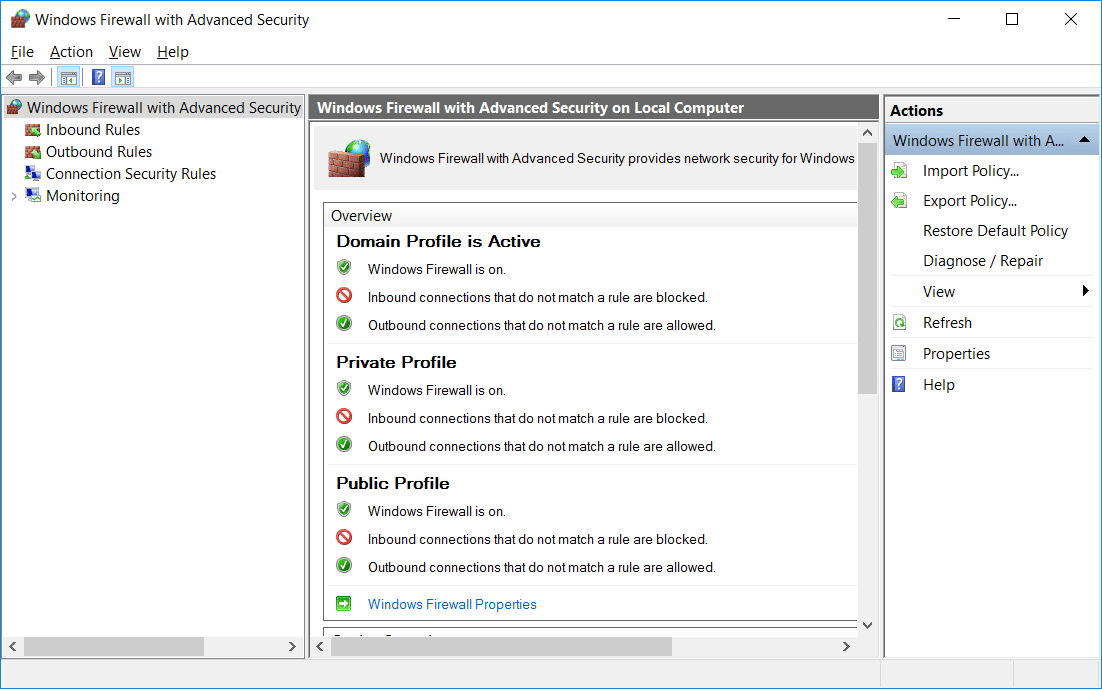
As mentioned above, we can open Windows Firewall with Advanced Security by clicking the advanced settings button in Windows Firewall. We can also run ‘wf.msc’ in either PowerShell or Command Prompt to open the advanced security interface directly. The image below shows the advanced security interface after opening.
On this window we can see an overview of the domain, private, and public profiles, which by default should all be enabled and blocking inbound traffic and allowing outbound traffic.
From the menu on the left we can select either inbound or outbound rules. As all outbound is allowed by default, we’ll focus on inbound rules here. Connection security rules can also be setup to configure IPSec connections, and monitoring can be used to log various firewall events.
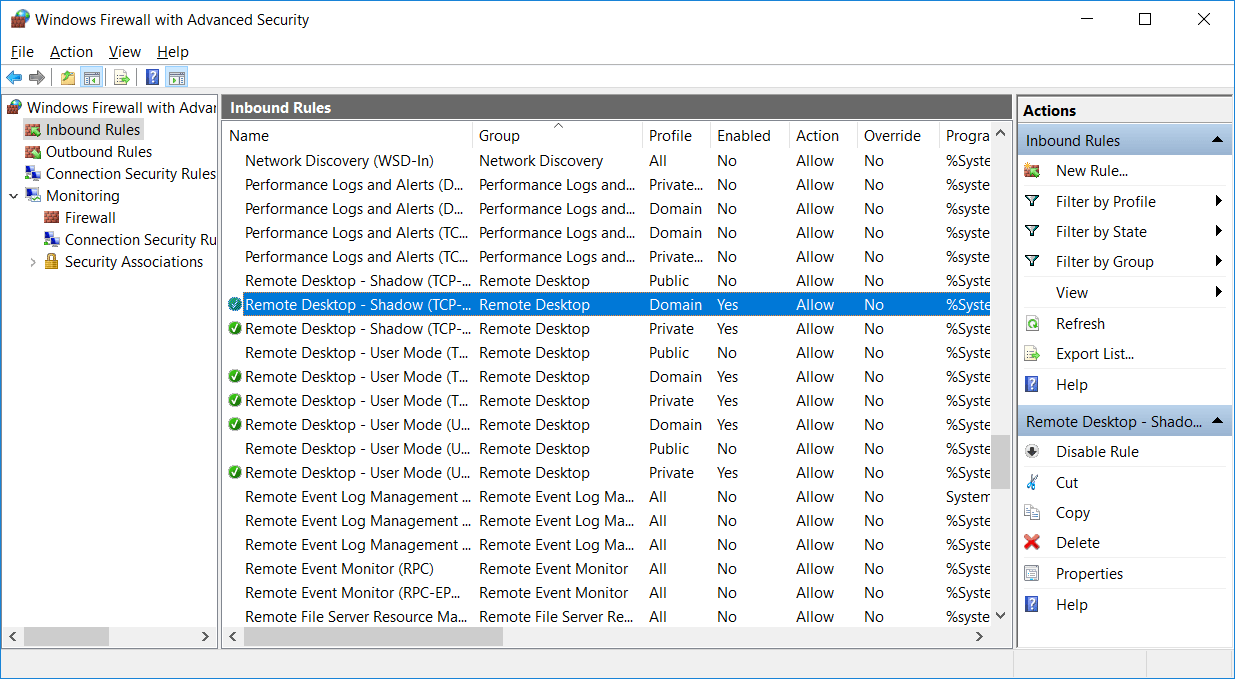
Under inbound and outbound rules we can view the rules that exist and that are currently enabled. These rules are available by default, rules with a green tick icon on the left are enabled and will allow traffic in while rules with no icon are disabled.
A rule that is disabled can be enabled by simply right clicking it and selecting enable. Likewise we can right click an enabled rule and change it to disabled. We can also view the properties of the rule by right clicking it and selecting properties. This will allow you to see what the rule is actually doing, including the ports that are being allowed through the firewall to specific programs, we’ll see this in more detail next when we create our own rule.
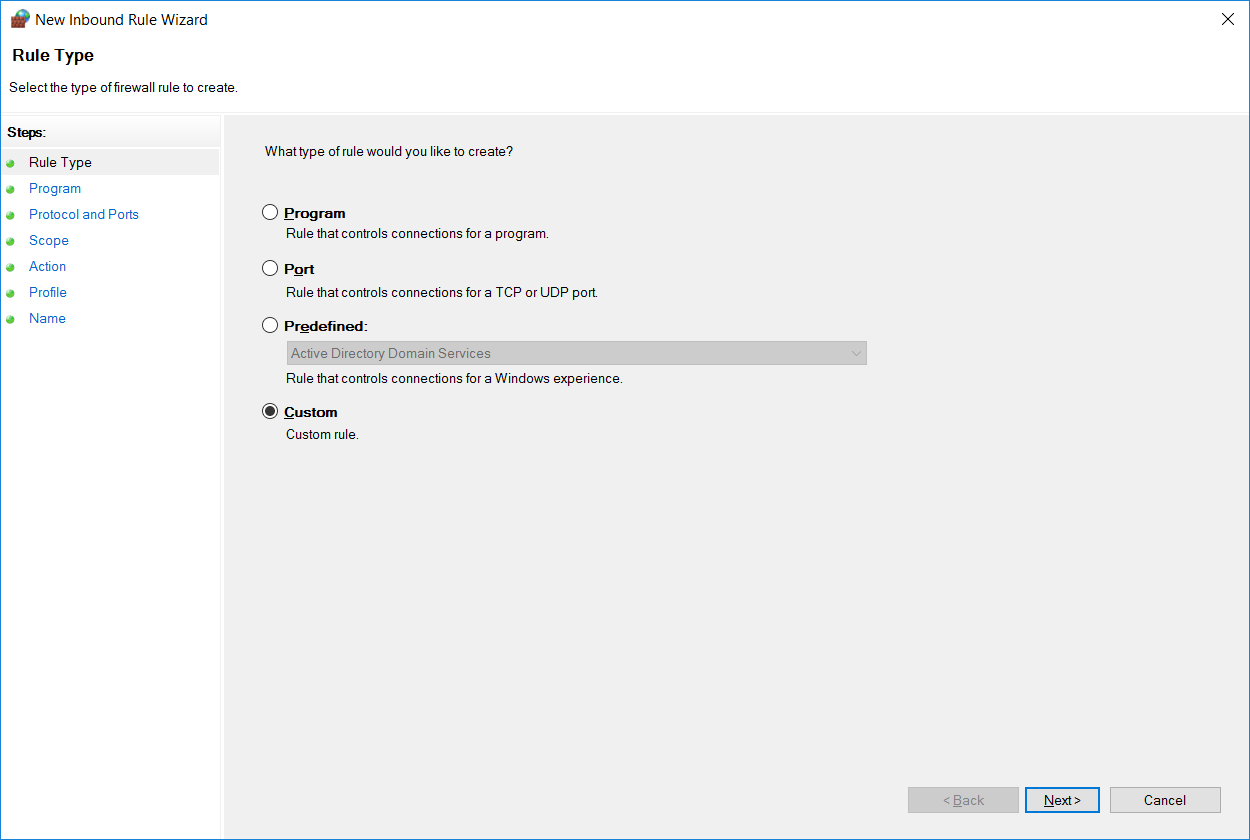
Create a Firewall Rule
Select Inbound Rules from the menu on the left and then select New Rule from the actions pane on the right. This will open the new inbound rule wizard. From here we can select if we want to create a rule for a specific program, to a specific port, or based off of an existing rule. In this case we’ll select custom as this gives us the most choice.
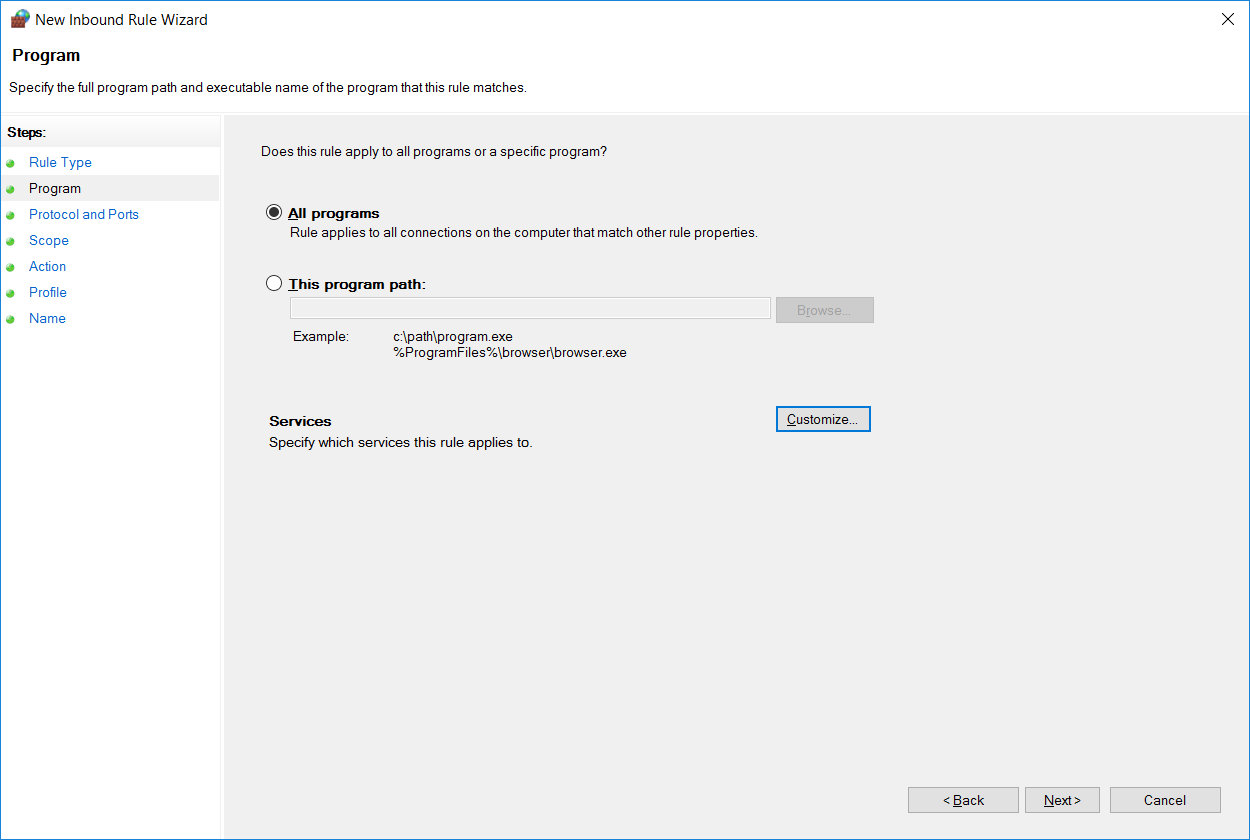
On the next screen we can select the specific program or service that the firewall should allow traffic in for. In this case we’ll just select all programs, however note that this can be used to further lock down a rule, rather than just allowing based on port/IP address we can also only allow traffic to a specific program.
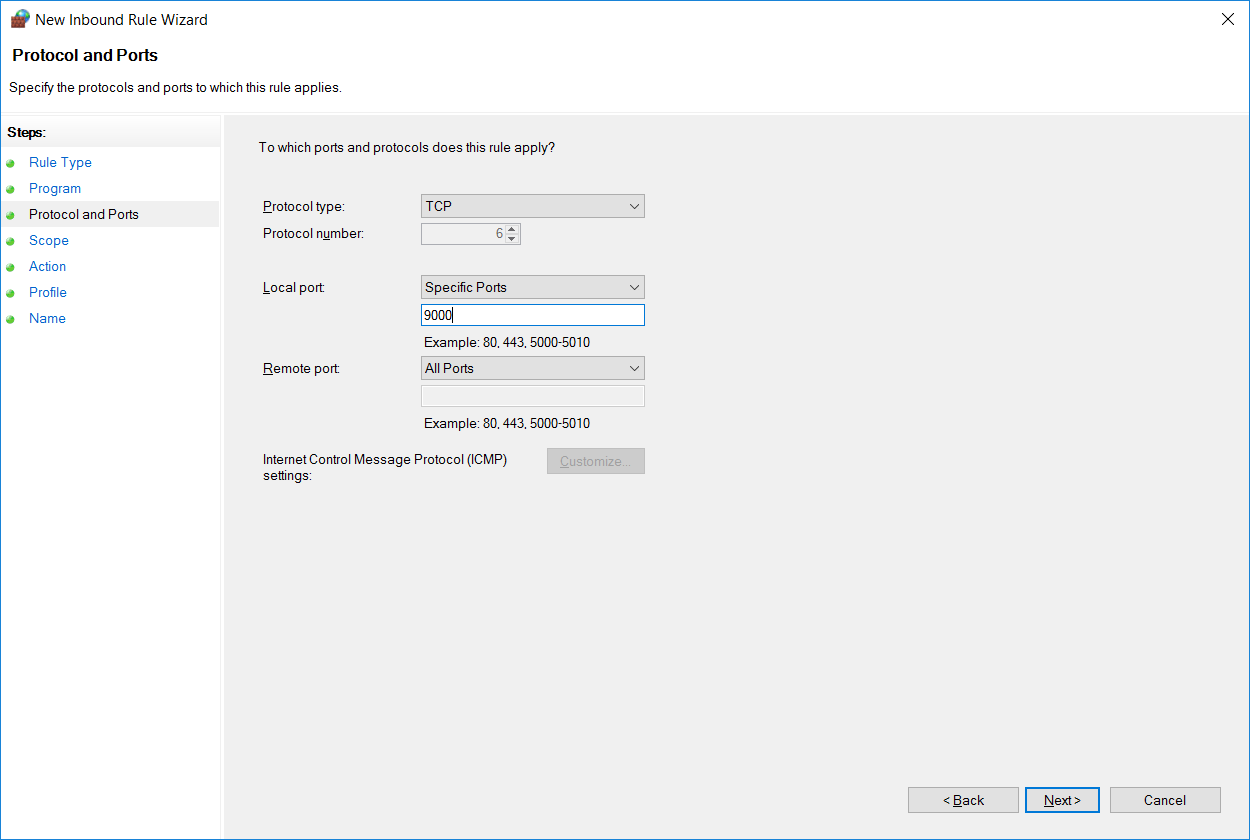
Next we can select the port and protocol that the rule should apply to. There are many different protocols to select from in the drop down, in this example we’re specifying that local TCP port 9000 should be allowed through the firewall. We use local port here as port 9000 is available locally on this server and listening for connections.
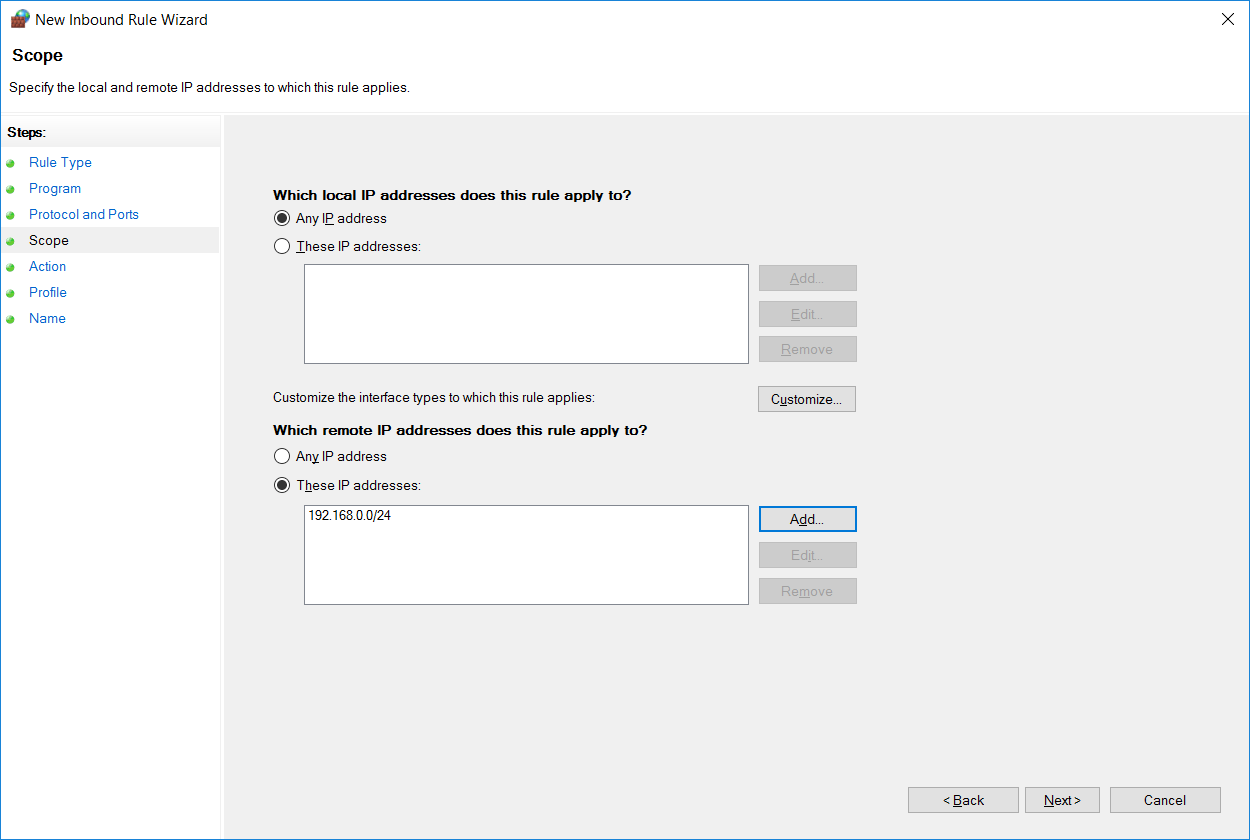
Now we can select an IP address or range of addresses that are allowed in through our firewall rule. In this case I’m allowing the remote address range 192.168.0.0/24 in through the firewall, so only this IP range will be allowed to connect to the server on TCP port 9000.
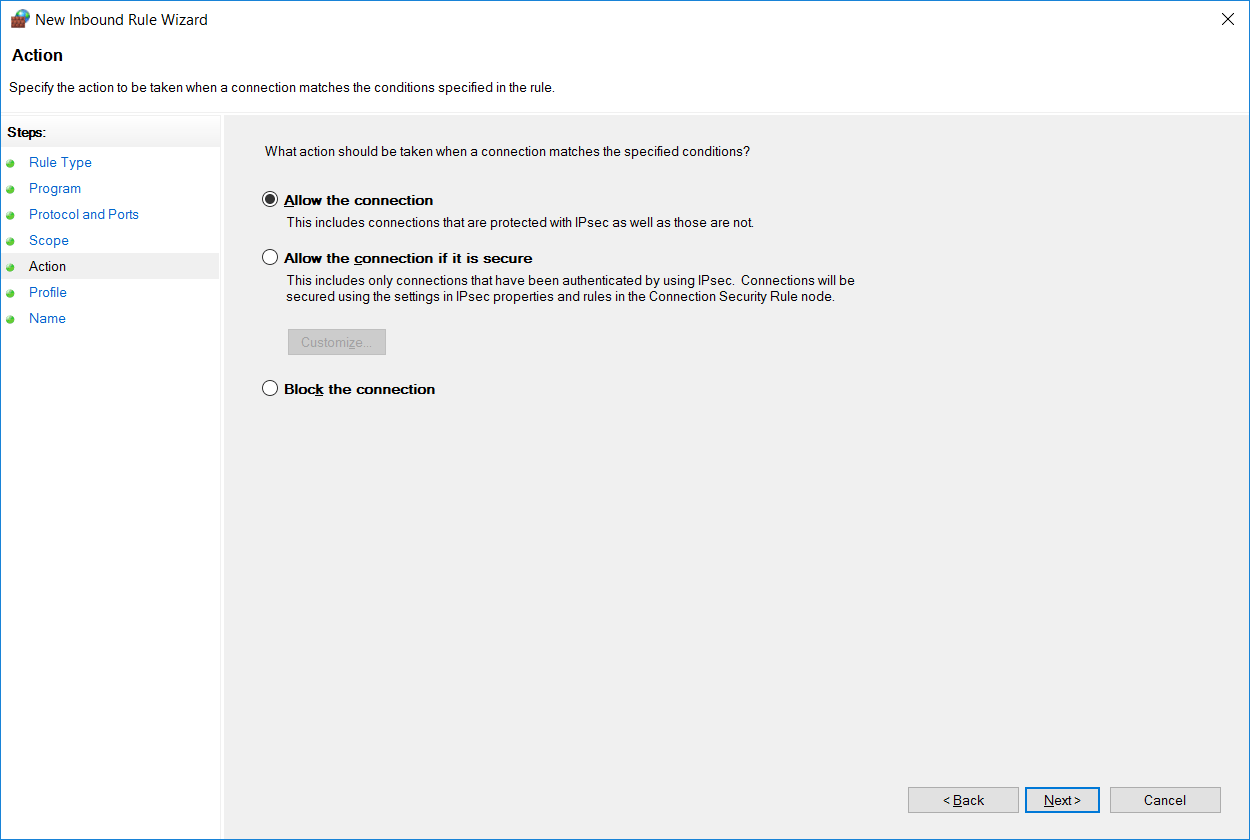
At this point we specify if we want to allow or deny the rule that we’re creating, we’ll leave this on allow as we want to let 192.168.0.0/24 in on TCP port 9000, however we could optionally explicitly block this instead. We could also optionally only allow the connection if it’s secure, which relies on IPSec being configured.
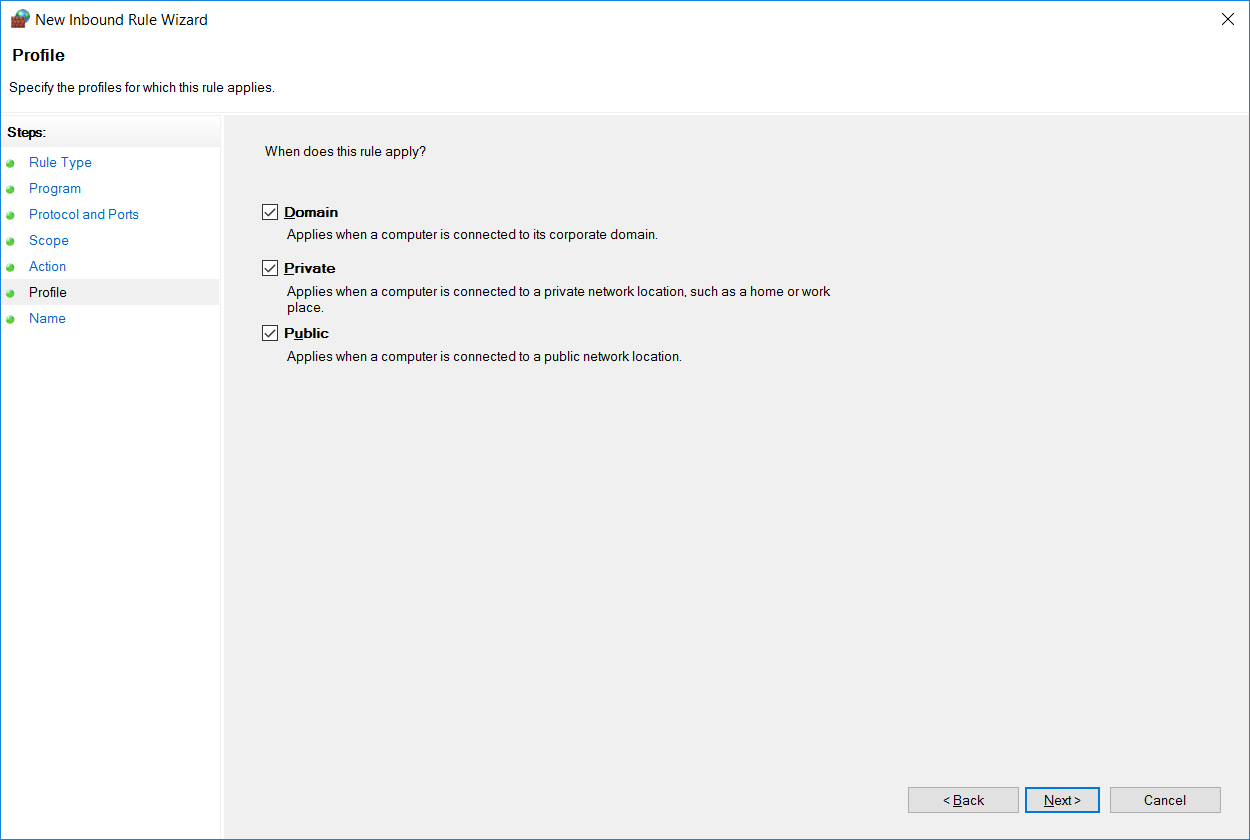
We can select which firewall profiles our new rule applies to. By default all profiles are selected, however you can change this as per your requirements.
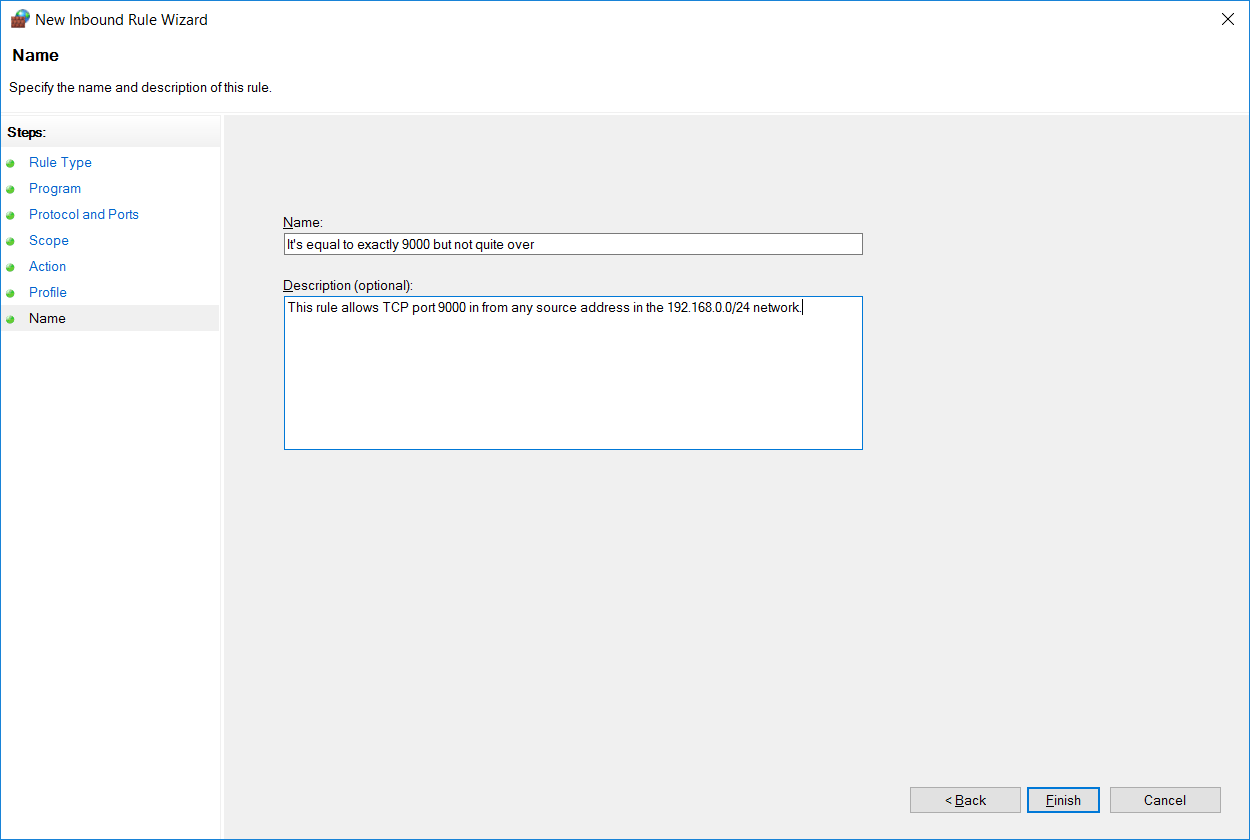
Finally we can specify a name and optional description to identify our rule. Once complete click finish, noting that as soon as you do this the rule will be live as per how you have configured it.
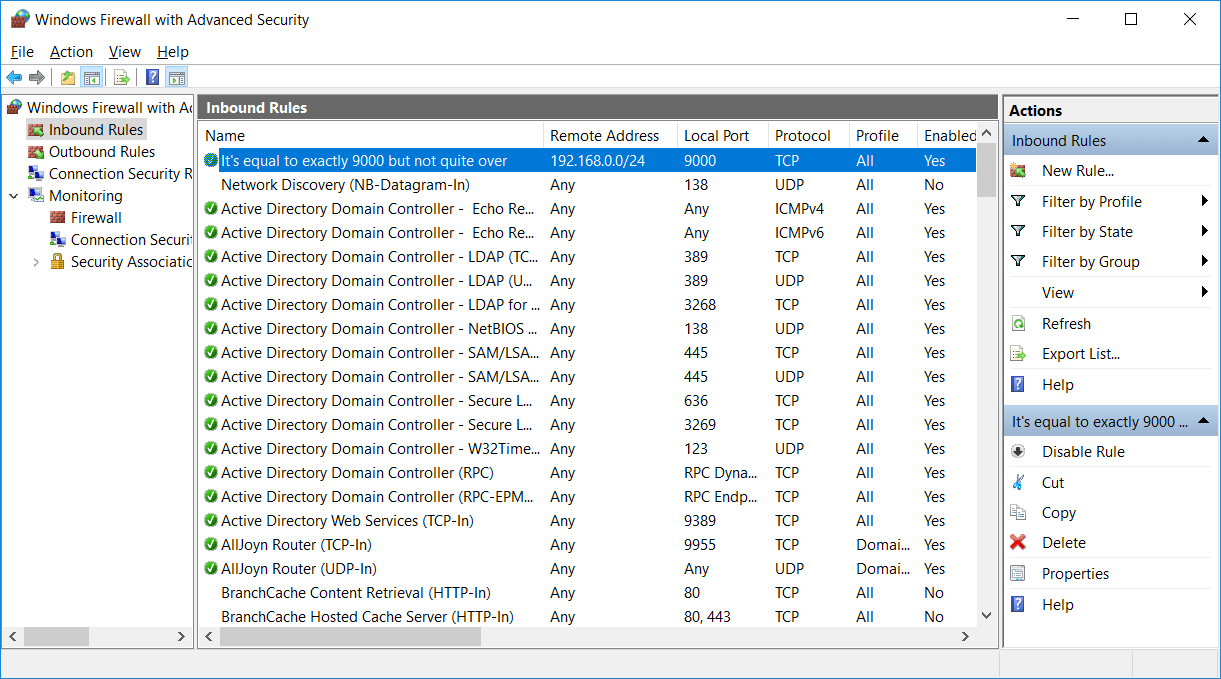
Our new rule will now show at the top of the inbound rule list above all of the default rules. We can identify it by it’s name and see briefly what it’s doing, it’s allowing the remote address range 192.168.0.0/24 into the local port 9000 with the protocol TCP on all profiles and is enabled.
By creating custom firewall rules such as this we can successfully configure windows firewall with advanced security.
Summary
We can configure very basic firewall rules with Windows Firewall, however Windows Firewall with Advanced Security is used to create much more custom and granular rules as we have seen here.
This post is part of our Microsoft 70-744 Securing Windows Server 2016 exam study guide series. For more related posts and information check out our full 70-744 study guide.
If a program rule allows all IP address but I block a certain address. Will that over ride the first rule
Yes, deny should come first ahead of allow.
would be great if you could also put what you did in this format r an admin level cmd like this
netsh advfirewall firewall add rule name=”it’s equal to 9000 but not quite over” dir=in remoteip=192.168.0.0 localport=9000 protocol=TCP action=allow enable=yes
just noticed i forgot to add the subnet /24 after the ip
I need windows firewall with advanced security