The Server Message Block (SMB) protocol is used to provide file and print sharing in a Microsoft based network. To help detect man in the middle (MITM) attacks that may modify SMB traffic in transit, we can configure SMB signing via group policy. By digitally signing SMB packets the client and server can confirm where they originated from as well as their authenticity.
SMB packet signing is available in all supported versions of Windows. Microsoft also note that depending on factors such as the SMB version, file sizes, and specific hardware in use, SMB packet signing can degrade the performance of SMB, which is to be expected as we’re signing every packet that goes across the network, which adds overhead.
It’s important to note that this is not encrypting the SMB traffic, we are only going to configure SMB signing so that the client and server can determine if SMB traffic has been modified. SMB encryption has been added as of SMB version 3.0 and newer.
This post is part of our Microsoft 70-744 Securing Windows Server 2016 exam study guide series. For more related posts and information check out our full 70-744 study guide.
Configure SMB Signing via Group Policy
To begin open up Group Policy Management, this can be done either through Server Manager > Tools > Group Policy Management, or by running ‘gpmc.msc’ in PowerShell or Command Prompt. At this point you can either create a new policy for SMB packet signing, or edit an existing policy.
Within the policy navigate to Computer Configuration > Policies > Windows Settings > Security Settings > Local Policies > Security Options.
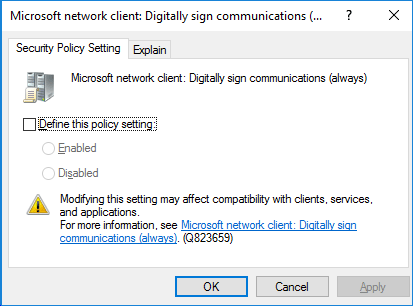
There are 4 policy items which we will cover below. All of these policy items can either be enabled or disabled. The policies all look like this when editing through GPME, you simply tick to define the policy setting, then choose between enabled or disabled. You can also view the Explain tab to get detailed information on what each option does.
SMB Server Packet Signing
The following two policy items apply to SMB server, that is Windows systems that serve out files or printers for instance over SMB to clients witin the network.
Microsoft network server: Digitally sign communications (always)
This policy option controls whether the server providing SMB requires packet signing, it determines whether or not SMB packet signing must be negotiated before further communication with an SMB client is allowed.
By default this setting is enabled for domain controllers, but disabled for other member servers within the domain.
Microsoft network server: Digitally sign communications (if client agrees)
This policy option determines whether the SMB server will negotiate SMB packet signing with clients that request it. With this setting enabled, the SMB server will negotiate SMB packet signing as per the request of the client. If SMB packet signing is enabled on the client then it will be negotiated by the server. By default this policy is only enabled on domain controllers.
SMB Client Packet Signing
The following two policy items apply to SMB clients, that is Windows systems that connect to an SMB server.
Microsoft network client: Digitally sign communications (always)
Enabling this policy ensures that the SMB client will always require SMB packet signing. If the server does not agree to support SMB packet signing with the client, the client will not communicate with the server. By default this policy is set to disabled, that is SMB is allowed by default without requiring packet signing. It is still possible for packet signing to be negotiated, it is just not required to operate.
Microsoft network client: Digitally sign communications (if server agrees)
This policy is enabled by default, and determines whether the SMB client attempts to negotiate SMB packet signing with the server. If this is instead set to disabled, the client will not attempt to negotiate SMB packet signing at all.
Microsoft no longer recommend using the “if server agrees” or “if client agrees” options, as these options only affect SMB version 1, which you may want to disable anyway.
Summary
We can configure SMB signing via group policy on both the server and client side. By default it’s primarily used on domain controllers in a domain, however by modifying the four policy items outlined above we can protect SMB traffic at the packet level.
This post is part of our Microsoft 70-744 Securing Windows Server 2016 exam study guide series. For more related posts and information check out our full 70-744 study guide.
0 Comments.