By default SMB version 1.0 is enabled in Windows Server 2016. As this was last needed in Windows XP and Windows Server 2003 it’s quite old, newer versions of SMB are more secure and have additional features. If you no longer need to support these older versions of SMB file shares, it’s a good idea to disable SMB version 1.0, or even remove it completely, as a number of recent vulnerabilities specifically affect SMB version 1.
Windows Server 2003 was the last supported version of Windows to only use SMB version 1, now that it’s no longer supported Microsoft are planning on shipping Windows with SMB 1 disabled by default. It’s currently enabled by default for compatibility reasons, however when we’re in a world where SMB 1 does not need to be supported it will not be used.
Just recently in March 2017 Microsoft patched a remote code execution vulnerability in SMBv1.
This post is part of our Microsoft 70-744 Securing Windows Server 2016 exam study guide series. For more related posts and information check out our full 70-744 study guide.
Audit SMB v1 Traffic
Before disabling or removing SMB v1, it’s worth checking if our network is actively using it, as turning it off could cause problems if it’s actually required.
We can audit SMB v1.0 traffic in our network to see if it’s still being used by running the following PowerShell cmdlet.
Set-SmbServerConfiguration –AuditSmb1Access $true
We can view this log by running the following PowerShell cmdlet.
Get-WinEvent -LogName Microsoft-Windows-SMBServer/Audit
You can also open event viewer and browse to Applications and Services > Microsoft > Windows > SMBServer > Audit. This is a good way of determining whether SMB 1 is still in use within your network before disabling it.
Disable SMB Version 1.0 Server Configuration
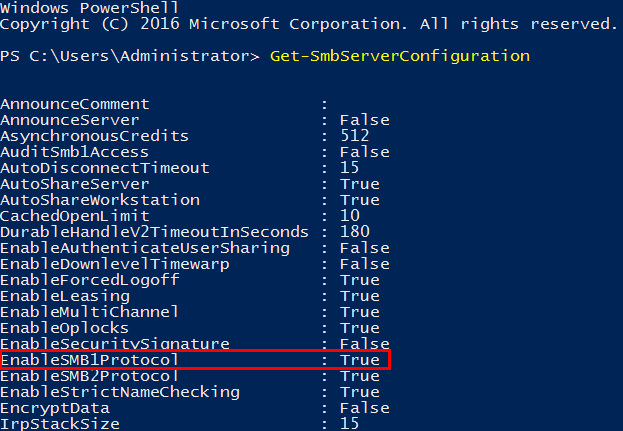
SMB can be disabled both on the server and client side. We’ll first start off by showing you how to disable SMB version 1.0 on the server side (the system that offers SMB shares). Open PowerShell with administrative privileges. If we run the ‘Get-SmbServerConfiguration’ cmdlet, we can see that by default EnableSMB1Protocol is set to True, as shown below.
Note that if you set AuditSmb1Access as shown previously that this value also shows in this output.
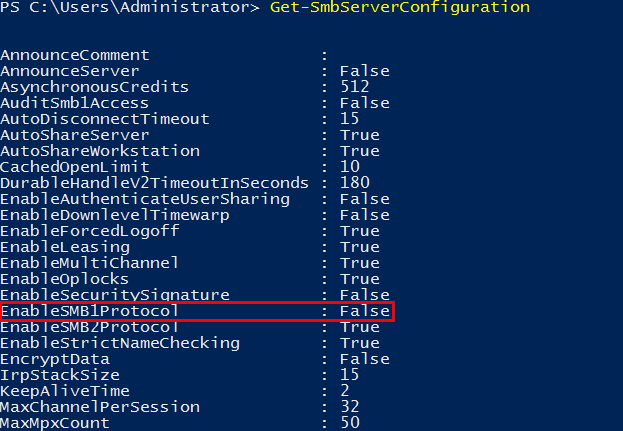
We can change this with the ‘Set-SmbServerConfiguration -EnableSMB1Protocol $false -Force’ cmdlet, as shown below.
We add -Force on the end otherwise we get prompted for confirmation, this allows us to simply run one command with no input required.
Now if we run the ‘Get-SmbServerConfiguration’ cmdlet again, we can see that EnableSMB1Protocol is now showing as False.
Remove SMB v1
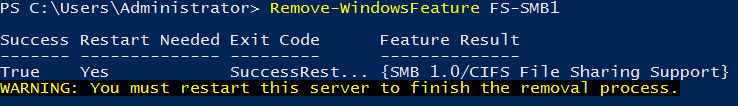
We can go a step further, and instead remove SMB version 1 from the server with the following PowerShell cmdlet.
Remove-WindowsFeature FS-SMB1
Note that this will require a system restart to complete.
This is a good step to do after you’ve had SMB 1.0 disabled for a while and are sure it’s not required.
Disable SMB version 1.0 Client Configuration
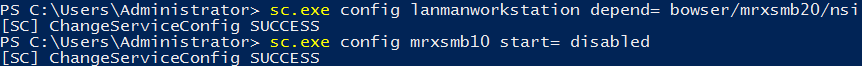
By disabling the server configuration as shown above, our server will no longer offer SMB v1 shares. The SMB client however is still able to connect to an external SMB v1 share on another server, unless we also disable the SMB v1 client. This is done by running the following commands.
sc.exe config lanmanworkstation depend= bowser/mrxsmb20/nsi sc.exe config mrxsmb10 start= disabled
Summary
With these steps you have now seen how to disable SMB version 1.0 in Windows Server 2016 on both the server and client side using Windows PowerShell.
Great article. Thank you.
If you follow your instructions “sc.exe config mrxsmb10 start= disabled” generated the following error:
[SC] OpenService FAILED 1060:
The specified service does not exist as an installed service.
Lol smb 1 is indeed VERY USEFULL it’s used by various non-windows based devices like Ps2, which won’t work with newer smb.
Useful != secure.
For the windows 10 workstations that come up in the audit log for still using SMB 1.0, how do I stop that? Manually disable SMB 1.0 on them and see if they can still login and access SMB shares?